Did you know that you no longer need to be a genius to hacker a telephone ?
Whether for protect your children Where prevent the best possible use of methods of the cybercriminals, Discover the most common techniques used to hack a smartphone in 2026!
Warning: this article does not encourage phone hacking.. It covers the various techniques used by hackers to hack a cell phone..
Among the most popular tools for hacking phones :
mSpy parental control application
EyeZy parental control application

1. Hack a phone with mSpy and EyeZy
mSpy and EyeZy are parental control applications designed for parents to monitor their children's phones.
However, it should be noted that some people use mSpy and EyeZy for malicious purposes, such as hacking into the phones of loved ones such as spouses or others.
1. Hack a phone with mSpy
How mSpy is used differs between the two operating systems (Android and iOS). As a tool dedicated to parents, it's easy to use and doesn't require no special skills in IT.
On Android
- The first step is to create an account on this site :
- Click on the Try it now green for create an account,

- Enter your e-mail address or continue with your Google account,
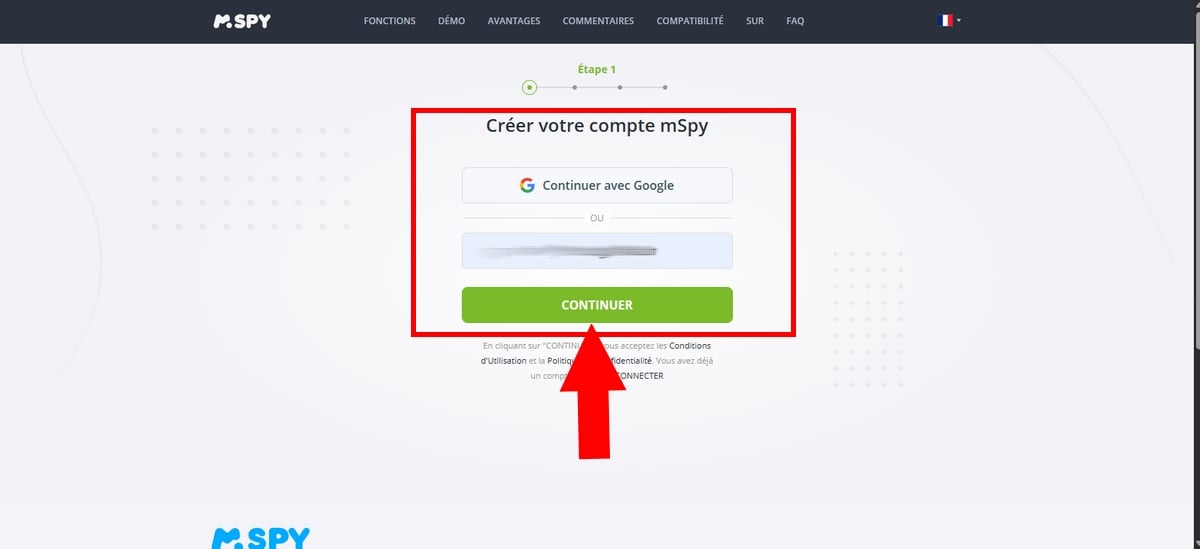
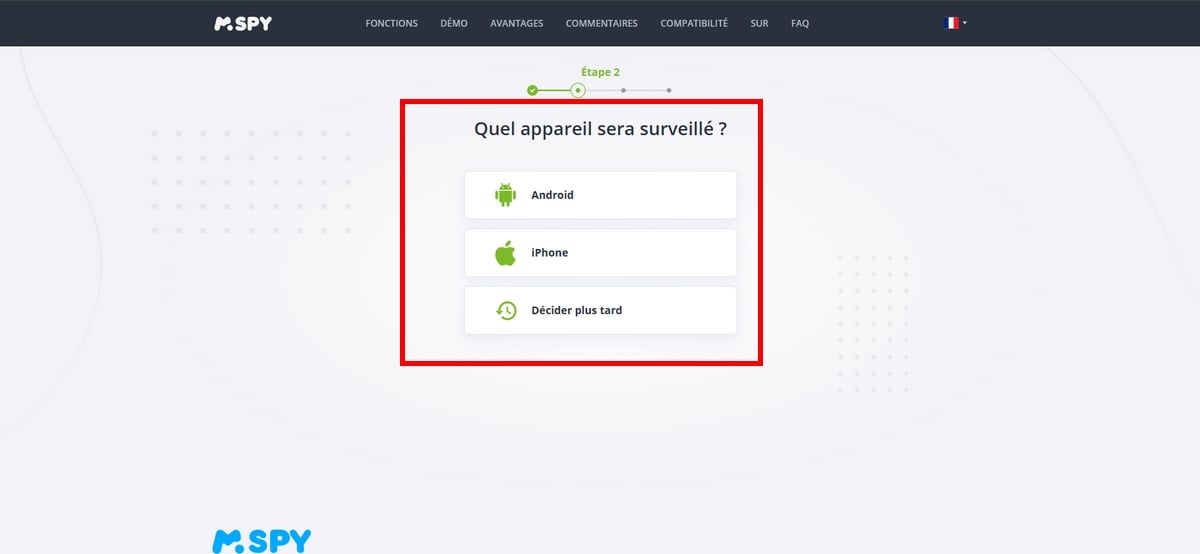
- Then choose android as the device to be monitored, but you can also decide this later,
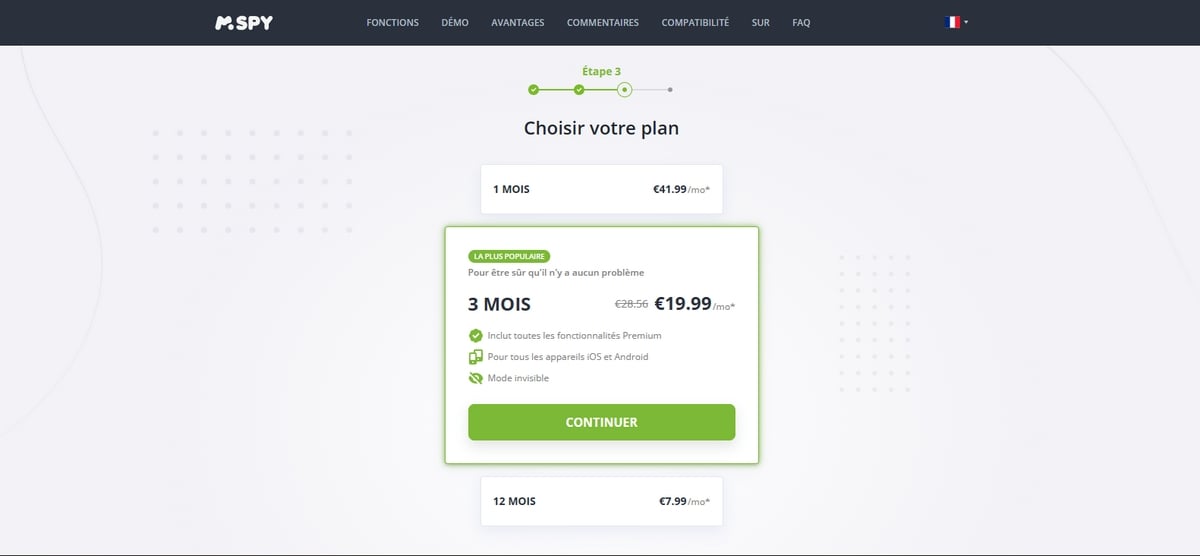
- Choose the rate that's right for you. If you'd like some advice on this subject, first find out about the various mSpy subscription prices !
- Have you made your choice? If you want to know whether mSpy offers a free version, If you have any questions, please feel free to take a look at our article!
- Add payment details. Then, once the purchase is complete, you'll receive an e-mail containing the configuration link, your password and your username will be sent to you.
- Let's move on to the next step! For this, you'll need physical access to the phone to be monitored.
Here's how Download and set up mSpy on the phone to be monitored :
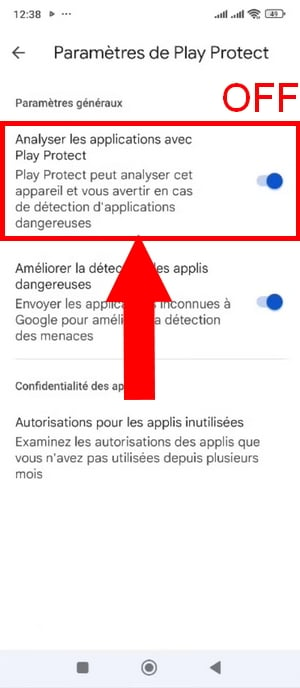
- Go to Play store, and deactivate the Play Protect function,
Profile on PlayStore ©Antonin for Alucare
- Select option Play Protect,
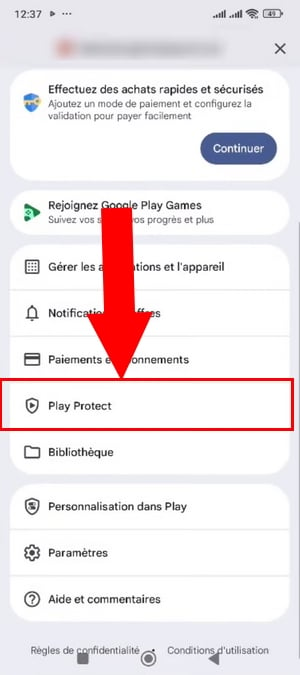
- Then click on the icon Settings at the top right of the screen,
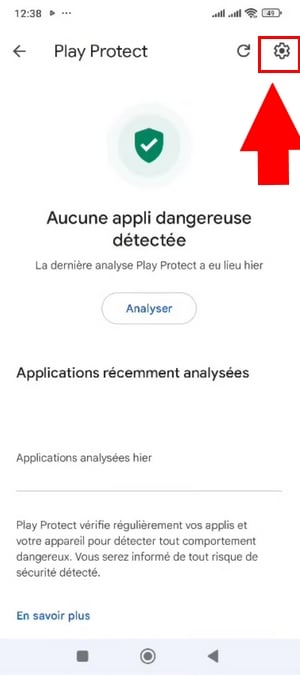
- Disable now function Play Protect and confirm this action by clicking on Disable.
- Download and install the mSpy application on the device to be hacked,
- Log in to your mSpy account to find out how to install it on your target phone.
On iOS
To use mSpy on iOS, you'll have 2 choices:
- iCloud synchronization (iCloud login and password required)
- WI-Fi Sync
These 2’using mSpy offer different functionalities.
a) Via iCloud Sync :
- Start by visiting this site to create your account and follow the steps to payment:
- Once you have taken out a subscription, choose iOS device, then choose the iCloud Sync installation method.
- Log in to your mSpy account using your login and password, sent by e-mail beforehand.
- Now, to monitor the target device, insert your iCloud credentials.
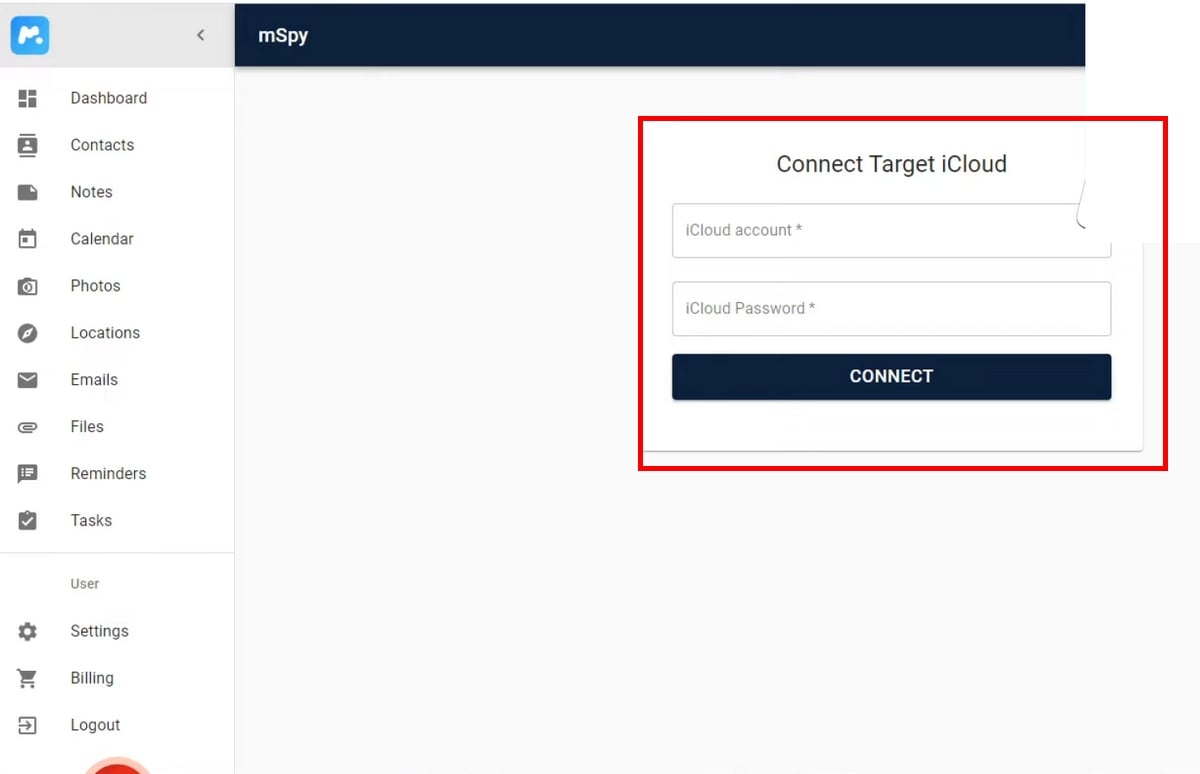
Insert your teenager's iCloud credentials ©Antonin for Alucare
- Two notifications will be sent subsequently, the first of which was sent to the e-mail address iCloud and the second to the target mobile device containing a 6-digit code.
- Insert the confirmation code sent to the target device on your mSpy account.
- Data collection will start and you should wait a few minutes to get all the data.
b) By WI-FI Sync
- When you have chosen a subscription, A link to download an additional application is included.
- Then install the WI-FI synchronization by clicking on this link, then connect the iPhone to keep an eye on Mac Where computer using a cable,
- Then launch the application on your computer and wait for the target phone's data to be backed up by it before disconnecting the iPhone.
- Finally, data on this iPhone will be visible on your personal account.
Note:
- The PC used and the device to be monitored must be connected to the same Wifi network to make it work.
Monitor a smartphone with EyeZy
EyeZy is another application of parental control designed for parents to keep an eye on their children.
However, some also use it in a roundabout way to hack a device and steal personal information of others.
Just like mSpy dedicated to parents, the use of the by EyeZy is easy and requires no special computer skills, but does require physical access to the phone to be monitored.
The steps are basically the same as with mSpy.
On Android
- start with create an account by clicking on the Try it now in pastel red here:

- Enter your e-mail address then Continue
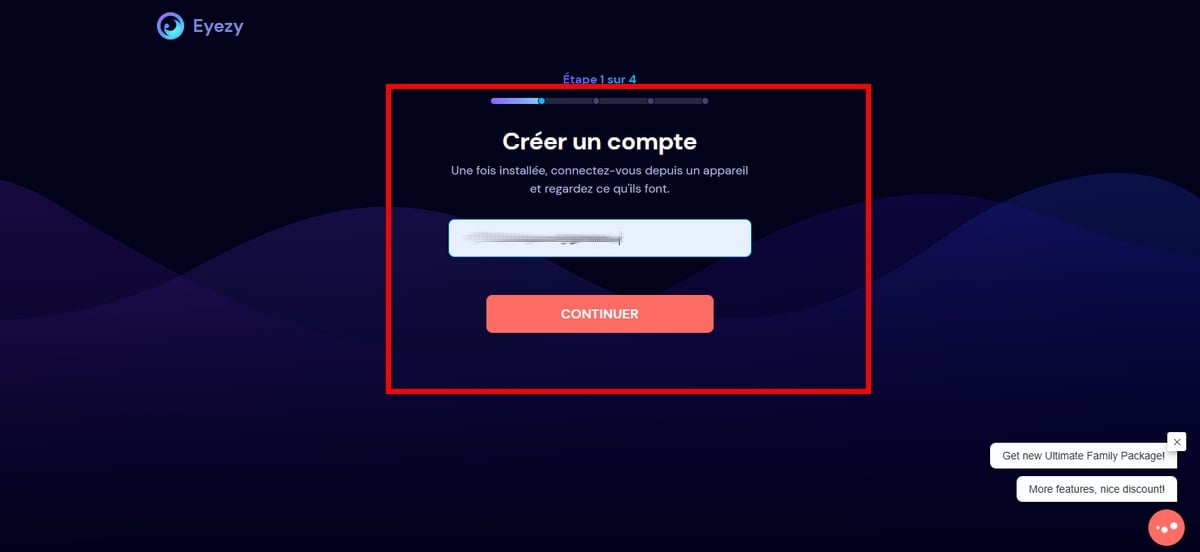
- Choose the device you want to monitor (Android Where iPhone),

- Now choose the subscription plan by clicking on Buy now. But first, if you like, discover the EyeZy subscription prices,
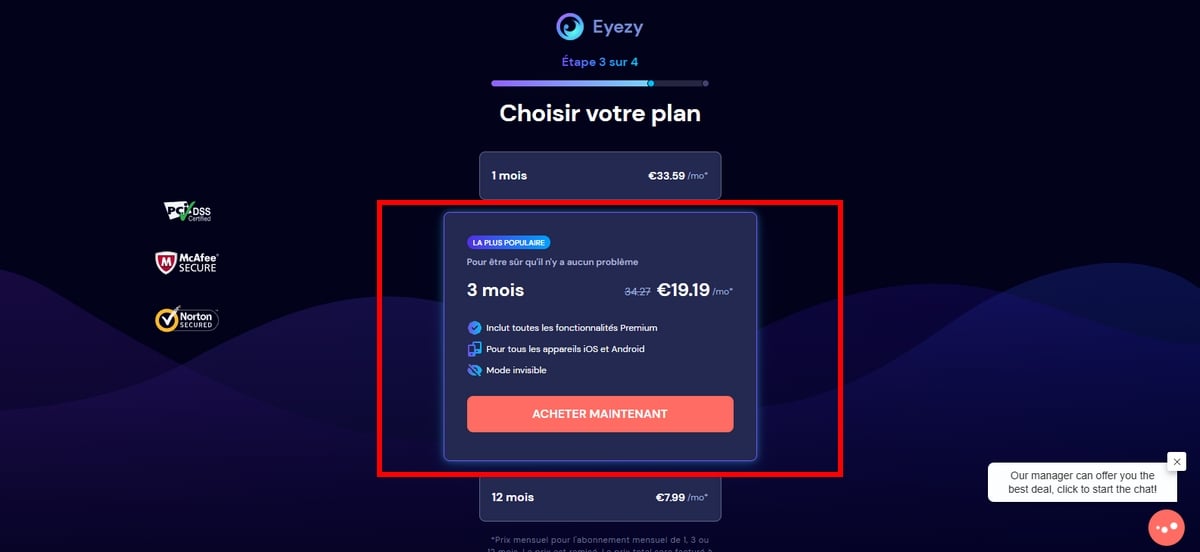
- Then add the payment details to complete the purchase of your EyeZy subscription.
Once you've made your purchase, go to your target device.
- Open Play store and deactivate the Play Protect,
- On the EyeZy account created, all the download steps required to install it on the target device will be displayed.
On iOS
First of all, please note that the following items are required for the following steps:
- The iCloud credentials of your loved one.
- A physical access to the relevant telephone.
a) Via WI-FI Sync :
- Once you have subscribed, please note that a additional application is added to it to install the synchronization application,
- Go to your dashboard, choose the version of your device,
- Then connect the target device to your computer Where Mac using a suitable cable,
- Once connected, the transfer will begin.
- Please do not unplug the phone until the backup is complete.
- Finally, your dashboard displays the various data present on your phone in real time.
b) Synchronization with iCloud
This installation method is just as easy, and takes just a few minutes!
- Log in to your EyeZy account on your private space, which you will obtain once payment has been made,
- Choose iOS as the type of device to be monitored,
- Then opt for the iCloud synchronization,
- You will be redirected to another login page where you must enter your iCloud credentials and password of your daughter/boy,
- Next, note that two posts will be sent simultaneously:
- One on the telephone at monitor
- Another on the email address linked to the iCloud account,
- Simply insert the confirmation code sent to the phone to be monitored on the EyeZy website.
In sum, mSpy and EyeZy require physical access to the device and/or knowledge of the target's personal credentials (i.e. identifiers iCloud and passwords).
| ✔️ About us | ▶️ mSpy | ▶️ EyeZy |
|---|---|---|
| Compatibility | Android/iOS | Android/iOS |
| Difficulty | Easy | Easy |
| Risk if used for malicious purposes | 3 years' imprisonment and €100,000 fine | 3 years' imprisonment and €100,000 fine |
| Efficiency | ⭐⭐⭐⭐⭐ | ⭐⭐⭐⭐⭐ |
Important reminder The use of these two tools must comply with the law.
2. Other (advanced) hacking techniques
What are the different piracy techniques used by hackers to sneak into your personal space?
a) Phishing

Prerequisites :
- Creation of website,
- A compelling message that inspires confidence.
This technique involves send fraudulent messages to your target, via e-mail or SMS (in this case, we call it smishing).
Requiring skills that are more advances in computer science, hackers pretend to be computer experts. trusted entities, such as a bank, a administration, a telephone service etc., reproducing the layout of authentic sites to appear more credible.
By clicking on the pictures where the links sent, the target will be redirected to a fraudulent site, almost identical to the original.
Next, the message must encourage him to enter your personal details (username and password), provided they are naive enough to do so. This is how hackers steal their victims' most important data.
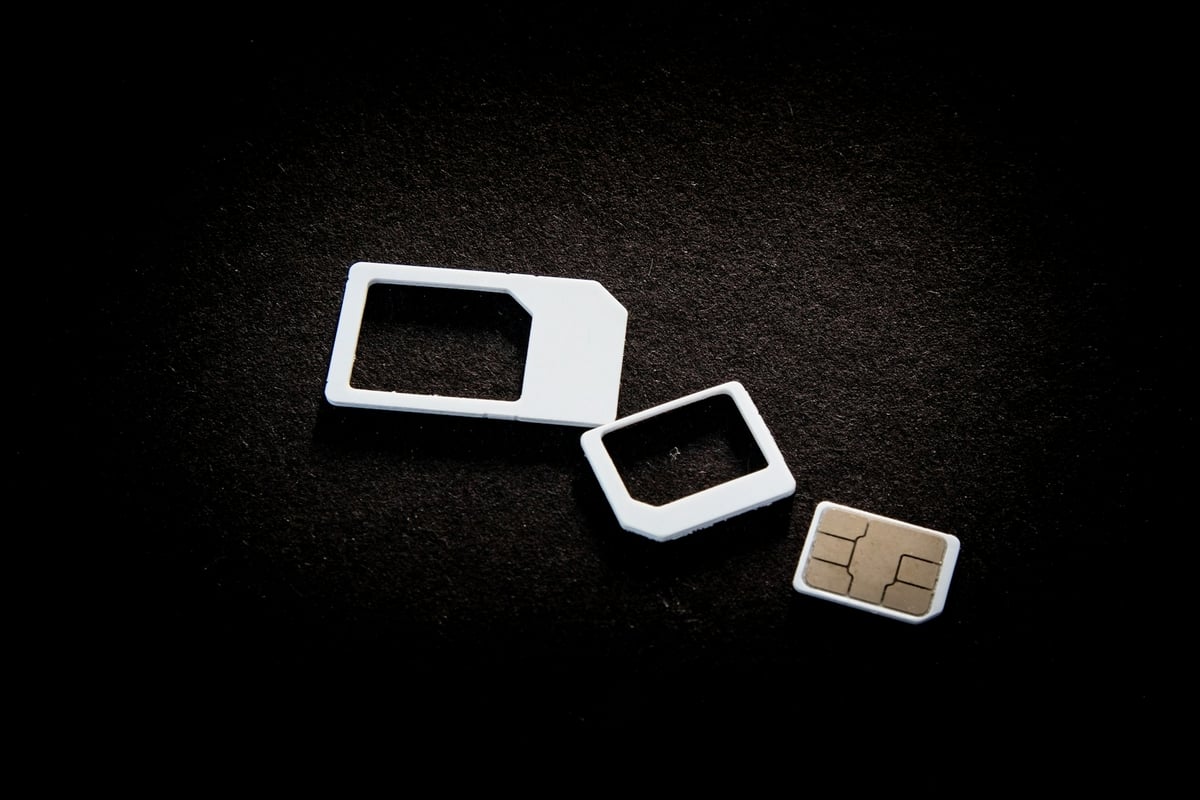
b) SIM card exchange
Prerequisites :
- Regarding the personal information on the target.
- The ability to convince the operator.
Hacking a SIM card occurs when a hacker pretends to be the target person to their mobile operator and convinced him to provide her with a new SIM card.
Once activated by the hacker, the old one will be deactivated. The hacker can then access all calls and messages, etc. on the new SIM card.
What's more, it can go even further, by exploiting accounts with some authentications at two factors, for example.
By knowing the login information, the codes of check will be sent to his phone instead of the victim's.
c) Keylogger
Prerequisites :
- Facility a application keystroke recorder on the target phone.
By downloading a keylogger, the hacker can track every keystroke on the keyboard in real time.
Often, these applications are hidden in free applications (games Where others) and are not available in official stores such as Apple Store or Play Store.
Thus, if the target downloads it onto his or her phone, the collection of the sensitive data becomes easier, such as passwords, them identifiers, without the target knowing anything about it.
d) Via WI-FI connection

Prerequisites :
- Be connected to the same wifi network than your target.
This method, often referred to as“man in the middle”is to connect to the same public WiFi network unprotected than the target.
As a result, the hacker can easily intercept certain sensitive information, such as calls, messages or authentication codes.
However, piracy via the wifi can be more or less ineffective if the person is using a vpn, The user does not connect to sensitive sites or make purchases.
By the way, if you want to use a VPN to protect yourself, such as Free NORDVPNclick on this article!
e) Via Bluetooth

Prerequisites :
- Special software to search for devices Bluetooth nearby.
Hackers can also use software designed to detect Bluetooth devices within a radius of 15 meters and connect silently.
This technique gives them access to all the information available on the hacked phone.
The hacker will be able to record conversations or geolocate the owner, device permitting.
f) Juice jacking
Prerequisites :
- Infect a terminal recharge public with malware.
The hackers can infect terminals of USB charging in public places with malware.
If the victim uses these terminals to recharge his phone, the virus spread on his device, allowing hackers to collect sensitive information.
However, these methods are not without risk! Find out more about the various legal consequences of these:
| ✔️ Techniques | ❓ Difficulty | ✅ Features | 👀 Risk | ▶️ Efficiency |
|---|---|---|---|---|
| the phishing | Quite difficult | Creation of a fake website and link. Based on naivety of the target | up to 5 years' imprisonment and a €375,000 fine (article 313-1) | Medium |
| L'SIM card exchange | Hard | The ability to cheat a operator | 5 years' imprisonment and €75,000 fine (article Art. 226-4-1) | High |
| L'keystroke recorder | Mean | Integrated into free applications, can be difficult to hide | 3 years' imprisonment and €100,000 fine (article 323-1 paragraph 1) | High |
| The wi-fi connection | Mean | Request a proximity to the target and specific tools | 1-year prison sentence and €45,000 fine (article 226-15) | Fairly low |
| the Bluetooth | Hard | A scope fairly limited (10 to 15 m) | 3 years' imprisonment and €100,000 fine (article 323-1) | Weak |
| the juice jacking | Hard | Ability to infect a physical USB port with malware in a public place. | 5 years' imprisonment and €150,000 fine (article 323-3) | Weak |
How do you know if your phone has been hacked?
As you may have guessed, spyware is installed on your device?
Run to this article on how to check if your phone is being spied on to find out!
How can you protect your smartphone against attacks?
Now that you know how hackers work, here's how to stay safe.
- Against spyware like mSpy and EyeZy: discover how to detect mSpy and EyeZy on your phone,
- Against the Phishing : don't never click on a link received by SMS, always check the sender and give preference to official sites,
- Against the Public WIFI Always use a vpn to encrypt your exchanges,
- Against the’SIM card exchange Ask your operator to activate a mandatory security code for all new card requests,
- Against the Juice Jacking Use your own mains socket at public charging stations,
- Against piracy via Bluetooth Bluetooth: deactivate your Bluetooth in public when you're not using it.
And for all your important accounts, don't forget to activate the’two-factor authentication (2FA).
FAQs
How can I hack into a phone remotely without holding it in my hand?
There are piracy software and hacking techniques that promise remote hacking, namely the phishing, the juice jacking, etc.
Some may require more IT skills than others, and the risks are high if you get caught!
How can I read the deleted messages on my son/daughter's phone?
It can be difficult to consult deleted conversations on a mobile device. Native features on certain phones can sometimes help.
On iOS :
- Messages ⇒ menu top right ⇒ Deletions.
If it is recoverable, you find the message in this section.
On Android :
- Messages ⇒ Three points or Menu at the top right of the screen ⇒ Messages still to come recoverable are available here.
Otherwise, some use spyware features such as EyeZy, that enable easily retrieve deleted conversations on their target's mobile device.
Can I see my browsing history even in private mode?
With parental control software such as mSpy, designed for parents who want to protect to their children, it is possible to consult their entire browsing history, even in private mode.
What's the best totally invisible spyware for your phone?
Among the best available tools on the market, many parents have placed their trust in mSpy and EyeZy to look after their children.
The reasons are as follows:
- They are well rated by users on review and download platforms. If you'd like to read reviews of these two services, check out the mSpy review and the game's opinion about EyeZy !
- They also have a active team who will answer any questions you may have about your account (24 hours a day).
- They are easy to use even for parents.
However, please note that this software was developed to keep an eye on children and teenagers, not to steal data from other people's phones.
Consequently, the use of this software for malicious purposes is prohibited by law.
How can I locate my child without receiving a location sharing notification?
Location-based applications such as geofinder send position-sharing notifications in order to function, but this is not the case for some programs such as mSpy and EyeZy.
Once installed on the phone you want to monitor, you can access their data with complete peace of mind. location.
Is it legal to monitor a minor child without his or her knowledge?
According to the’article 371-1 of the French Civil Code, A parent's role is to protect his or her children. However, a child, even a minor, also has a right to privacy.
So, if you want to help them by installing spyware on their phone, it is strongly recommended to dialogue with your children about the situation and your reasons for it.
Consult the CNIL website to find out more about your obligations as a parent and better understand the balance between security and privacy.
En somme, pour access a cell phone, There are common software and hacking techniques used by hackers.
It is important not to overlook the fact that these tools represent a breach of privacy and are prohibited by law.
Once again, it should be remembered that the aim of this article is to provide information on the various techniques for pirate a phone to protect you as best we can.
If you have any questions or comments, don't hesitate to ask!




For all that is needing the opportunity to spy or hack a phone and see all of its information, it can be possible to view all the messages, call logs, live location, shared media and notes, access to entirely everything from target device.
It's simple to understand and operate .
A very good way and contact to reach when needing all hacking and spying access to devices.
🥲
🥲
Molto interesting il tuo sito!
Is it possible to install a remoto?
E chi fa questo lavoro?
You have :
https://www.alucare.fr/Mspy/
https://www.alucare.fr/Eyezy/
and not possible remotely